As humans, we have always thrived to find smarter ways of using the tools available to us. The Google search engine is one such example where it provides results to billions of queries daily. This page covers all the Google Dorks available for SQL Injection, Credit Card Details and cameras/webcams in a List that you can save as a PDF and download later.
As interesting as this would sound, it is widely known as “Google Hacking“. It combines different search queries to look for a very specific piece of data that may be interesting to you. The information shared below is only for White hat purposes only.
About Google Dorks and what they are used for
This is a search query that is used to look for certain information on the Google search engine. These are developed and published by security thieves and often used in Google hacking.
These are very powerful. They allow searching for a variety of information on the web plus can also be used to find information we did not even know existed.
Since they are powerful, they are often used by security criminals to find information regarding victims or information that can be used to exploit vulnerabilities in sites and web apps.
Google search engine is designed primarily to crawl anything over the web and all this helps to find:
- Text, images, news, videos and a plethora of information.
- As it has a tremendous ability to crawl, it indexes data along the way, including sensitive information like login credentials, email addresses, sensitive files, site vulnerabilities and even financial information. In most cases we being users won’t be aware of it.
How to use Google Dorks Cheat Sheet (Explained)

For this, you need to type the below queries in the search box on Google and hit enter. Following are some of the best queries that can be used to look for specific for information:
10 Google Dork Popular Query Examples
- Inurl:.give “register forum” – This one is used to search for sites on .gov domains which carry the words “register forum”. It searches for governmental sites that allow registering for a forum.
- Inurl:.edu “register forum” – This one is used to search for sites on .edu domains that carry words “register forum”. It searches for school sites that allow registering for a forum.
- Inurl:.com “powered by vbulletin” – This one is used to search for sites on .com domain which carry the words “powered by VBulletin”. It searched for sites that run on this forum software.
- “powered by vbulletin” inurl:.mil – This one is used to search for sites on .mil domain which carry the words “powered by vbulletin”. It searched for military sites which run on this forum software.
- “powered by vbulletin” inurl:.edu – This one is used to search for sites on .edu domain which carry worlds “powered by vbulletin”. It searches for school sites which run on this forum software.
- “powered by vbulletin” site:.mil – This one is used to search for sites on .mil domains which carry words “powered by vbulletin”. It searched for military sites which run on this forum software.
- “powered by vbulletin” site:.gov – This one is used to search for sites on .gov domains which carry words “powered by vbulletin”. It searches for government sites which run on this forum software.
- “powered by vbulletin” site:.edu – This one is used to search for sites on .edu domain which carry words “powered by vbulletin”. It searches for sites that run on this forum software.
- Inurl:edu “login” – This one is used to search for sites on .edu domains with the words “login”. It searches for school sites that contain login information.
- Site:.edu “phone number” – This one is used to search for sites on .edu domains with the words “phone number”. Student “phone number” – it searches for sites on .edu domains that carry words “student” and “phone number”.
RECOMMENDED: Search Engines that are useful for Hackers.
Google Dorks For SQL Injection purposes (SQL Dorks)

Scraper API provides a proxy service that is designed for web scraping, so you can complete large scraping jobs quickly without having to worry about being blocked by any servers plus it has more than 20 million residential IPs across 14 countries along with software that handles JavaScript able to render and solve CAPTCHAs.
- Cache
(cache:www.google.com web) shall show the cached content with the word “web” highlighted. This function can also be accessed by clicking the “cached” link on its main result page. The query (cache:) shall show the web page version it has on its cache. Like (cache:www.google.com) shall show Google’s cache for its homepage.
- Link
(link:www.google.com) shall list webpages that carry links to its homepage.
- Related
(related:www.google.com) shall list webpages that are similar to its homepage.
- Info
(infor:www.google.com) shall show information regarding its homepage.
- Define
Query (define) shall provide the definition of words you enter after it, which are collected from different online sources. The definition shall be for the complete phrase entered (it shall have all words in exact order typed) like (define:google)
- Stocks
If you begin the query with (stocks:) operator, Google shall treat the rest of the query terms as stock ticker symbols and link to a page showing information for symbols. Like (stocks: intc yhoo) shall show information regarding Intel and Yahoo
Note: You need to type in ticker symbols, not the company’s name.
- Site
If you include (site) in the query then it shall restrict results to sites that are given in the domain. Like (help site:www.google.com) shall find pages regarding help within www.google.com. (help site:com) shall find pages regarding help within .com URLs.
Note: There should be no space between “site” and domain.
Download SQL Dorks PDF:
SQL Injection Dorks [PDF Document]
ALSO READ: Try these Hilarious WiFi Names and Freak out your neighbors.
Google Dorks for Credit Card Details (New)

Credit Card details are one of the most valuable pieces of data that an entity with malicious intent can get its hands on. Below are some dorks that will allow you to search for some Credit or Debit card details online using Google.
allintitle
If you begin a query with (allintitle) then it shall restrict results to those with all of the query words in title. Like (allintitle: google search) shall return documents that only have both “google” and “search” in the title.
intitle
If you include (intitle) in the query then it shall restrict results to docs that carry that word in title. Like (infinite:google search) shall return docs that mention the word “google” in their title and also mention the word “search” anywhere in the doc (title or no). Putting (intitle:) in front of each word in the query is equal to putting (allintitle:) in front of the query: (intitle:google intile:search) is the name as (allintitle: google search).
allinurl
If a query begins with (allinurl:) then it shall restrict results to those with all query words in url. Like (allinurl: google search) shall return only docs which carry both “google” and “search” in url. It ignores punctuation to be particular, thus, (allinurl: foo/bar) shall restrict results to page with words “foo” and “bar” in url, but shall not need to be separated by a slash within url, that they could be adjacent or that they be in that certain word order. For now there is no way to enforce such constraints.
inurl
In the query if you add (inurl:) shall then it shall restrict results to docs carrying that word in the url. Like (inurl:google search) shall return docs that mention word “google” in their url and also mention “search” anywhere in the doc (url or no). If you put “inurl:” in front of each word of the query is equal to putting “allinurl:” in front of query: (inurl:google inurl:search) is the same as (allinurl: google search).
Now the search service never intends to get unauthorized access of data but nothing can be done if we keep data in the open and do not follow proper security mechanisms.
Emails, passcodes, usernames, financial data and others should not be available in public unless it is meant to be. Our bank details are never expected to be available in the Google search bar whereas our social media details are available in public as we allow them.
Google Dorks for Credit Card Details [PDF Document]
ALSO READ: Vulnerable SQL Injection Sites for Testing Purposes.
Google Dorks for Online Cameras, CCTV

Security cameras need to be connected to the internet to have a know-how on what is going on in the area you live, the moment you connect any device to the internet someone can get access to it hypothetically. You can use Google Dorks to search for cameras online that have their IP address exposed on the web and are open to the public.
This scary part is once it is compromised, a security theft can make some lateral moves into other connected devices.
After this, he/she can:
- Disable alarm systems.
- Hack into the system.
- Torment one house by blasting music.
- Turn on the Television and whatnot.
All this and a lot can happen as long as it is connected to the same network. Below are some Google Dorks that can help you discover some Webcams or Cameras that are exposed online.
Download Camera/Webcam Dorks:
Camera and WebCam Dork Queries [PDF Document]
Secure your Webcam so it does NOT appear in Dorks searches:
Passcodes MUST be complex
Do not use the default username and password which come with the device. Change it to something unique which is difficult to break. Avoid using names, addresses, and others. We suggest using a combination of upper and lower-case letters, numbers, and symbols.
Change passwords frequently
Never hold onto one password for a long time, make sure to change it.
Keep their firmware up-to-date
Make sure to keep your software up-to-date as this shall help to patch vulnerabilities in software that allow security hackers to access the device. Vendors of surveillance expect users to update their devices manually. So, check to see if you have an update available. Set up manual security updates, if it is an option.
Install a Firewall
This is a network security system that keeps all the bad guys out. It does not have to be dedicated you can also use open-source Firewalls that are free. You don’t need expensive and paid ones such as Cisco-ASA or F-Secure.
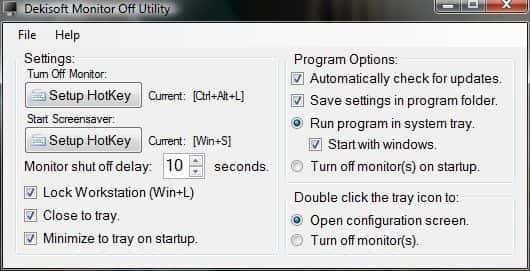
Full Disclaimer: Please use these only for educational and informational purposes only. We do not encourage any hacking-related activities. DekiSoft will not be responsible for any damage you cause using the above information.
Conclusion – Are you using any Google Dorks?
This was our extensive article on Google Dorks Cheat Sheet that you can use mainly for SQL Dorks and finding Credit Card Details. There are also some Dorks shared for cameras and webcams that can be accessed by an IP address. You can also save these as a PDF to download. Let us know which ones are you using and why below in the comments.