njRAT (Bladabindi) is a highly sophisticated remote access tool (RAT) or Trojan with which the holder of the program can control the end-user system. It was originally founded back in 2013 with a few variants traced back to 2012 as well. Currently, you can find the download of njRAT for free below. It was made by hacking an organization from various countries known as Sparclyheason and was used against targets in the Middle East. Spread this through infected drivers and phishing.
History of njRAT (Bladabindi)
Many attacks were reported back in 2014. In an attempt to disable it capabilities, 4 million sites were taken down while making an attempt to filter traffic via no-ip.com domains.
By 2016, Softpedia reported that spam campaigns that were spreading like njRAT were targeting discord. In 2020, it also reported the appearance of a cracked VMware download that would get this through Pastebin. Terminating the process would crash the system.
In 2017 an Islamic site was hacked to display a fake Adobe Flash player update download, which downloads the Trojan instead.
njRAT v0.7 New Features

- Steal passcodes that are stored in web browsers or in other apps.
- Log keystrokes.
- Record systems camera and microphone.
- Manipulate the system registry.
- Open the process manager to kill different processes.
- Open a remote shell which allows the attacker to use the system command.
- Manipulate files.
- Able to remotely execute the file from a URL or disk.
- It remotes into the victim’s desktop or active window.
- See IP address, system name, username, OS, install date as well as the country of the victim.
- Remote control and view.
- Remote shell.
Often targeting people and organizations, it has been observed as delivered through malicious unsolicited email (malspam) campaigns also within weaponized versions of legitimate software. Moreover, reinforcing the adage that there is no “hour among thieves” weaponized versions of malicious tools including RAT itself, copyright-infringing downloads, like the ones which are obtained through peer-to-peer file-sharing networks, have been used to deliver this to other unscrupulous users.
ALSO TRY: Download OctoSniff Free XBox and PSN Resolver
How njRAT is delivered and Infects other devices

Infected advertisement campaigns
These are culminating the installation of this were seen in 2010 as utilized a common shipment tracking theme, mimicking the popular postal services to deliver zip compresses archive attachment which carries an encoded visual basic script known as VBE payload.
It sends a 10-character random string through an HTTP post to the command and control (C2) server which responds with base64 data that along with the string is saved there in the windows registry key. VBE payload downloads its executable for a hard-coded URL which is saved within the victim’s startup directory for persistence before being launched.
Malicious Installer files
Masquerading this as a legitimate apps installer uploaded to the file-sharing services, victims downloading content from unofficial sources risk receiving from njRAT along with their desired app.
Once executed, installation proceeds in the foreground while visual basic and PowerShell scripts, or an executable, are dropped into the startup directory of the victim for persistence and launched to download this payload.
Now to evade detection, an encoded, obfuscated and encrypted njRAT payload acting as an image file is hosted on file-sharing services like Microsoft OneDrive and DropBox. This is used to reduce the likelihood of blocking or detection, especially given the use of service often utilized within the enterprise and appearing as a benign file type that may not be subjected to inspection.
Once it is downloaded, it is decoded and decrypted to a legitimate process and launched.
Command and Control Server (C&C)
Having been compromised through one of the different delivery methods, its victim’s machines shall call home to threaten the actor’s C2 server.
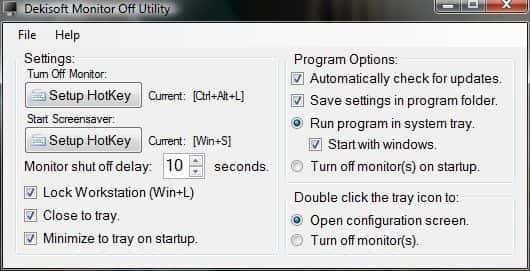
Provided as web-excusable and not requiring any certain server configuration unlike the web-based threats, it provides a simple C2 interface that allows the threat actor to interact easily with the victim machines.
Now, based on recent observations, many threat actors deploying this appear to favor Dynamics DNS (DDNS) hostnames and by doing this they can update the IP address of C2, to which the DDNS hostname dissolves, without any need to rebuild and redistribute this payload.
Payload Builder
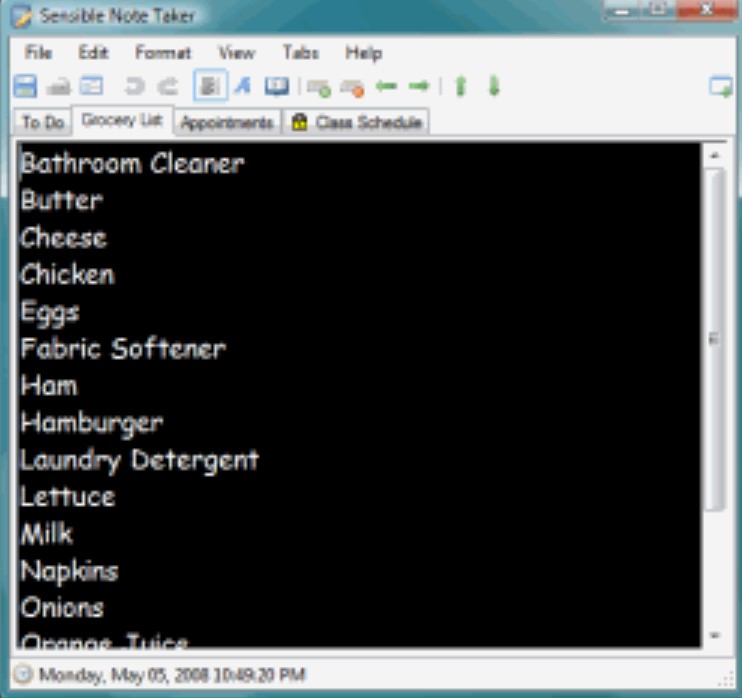
Easy to use builder app provides a simple interface through which payload can be configured.
In addition, to be able to configure malicious executables’ appearance and persistence method, through the windows startup folder or the registry key, C2 hosts allow the threat to “call home” to the C2 component.

The final delivery method depends upon the sophistication of the threat actor, especially provided that its toolset does not appear to provide any packer or cryptor.
As there are some as-a-service offerings on underground forums and marketplaces like offering to provide pre-built “undetectable” njRAT payload and preconfigured C2, lower ones might attempt to deliver “built” executables to victims that shall be detected by endpoint and network security solutions.

Ones paying for access to pre-configured services or those with great capabilities employ evasion tactics like encrypting, packing malware binary and crafting convincing lures which maximize the chance of a successful campaign.
ALSO TRY: Download Sentry MBA (Latest Release) for Windows and Linux.
Safety Tips for njRAT
- Consider preventing the execution of script interpreters like PowerShell and VBScript to prevent misuse.
- Download apps from trustworthy sources.
- Educate users on the difference between legitimate and malicious URLs like the use of DNS services or typo-squat domains.
- Educate users on the risks of opening attachments from unknown and unsolicited emails.
How njRAT does not get detected by antiviruses
It comes with some tricks to avoid detection by anti-virus software like it uses multiple .NET obfuscators to obstruct its code. Another technique it uses is disguising itself into a critical process, blocking the user’s ability to shut it down, thus making it hard to remove from infected systems. Bladabindi RAT is similar to AndroRAT and also deactivates processes that belong to anti-virus software which allows it to stay hidden. Moreover, it knew how to detect if it is running on a virtual machine which helps the attacker to set up countermeasures against all the researchers.
To spread, it can detect external hard drives which are connected through USB. Once a device like this is detected, it shall copy itself on the connected drive and create a shortcut.
Update: We have now also included the danger edition of njRAT. This includes more modules that help it evade antivirus detection and provide support for Android with an APK.
Download njRAT Free Latest Version 2024 (Windows 10/11 & Kali Linux)
Bladabindi has been around for many years and is known as njRAT download too. It has been recently updated with newer releases such as 0.7, 0.7d and 0.8d. All of these bring massive improvements in antivirus evasion
njRAT Download v0.7/v0.7d (Latest)