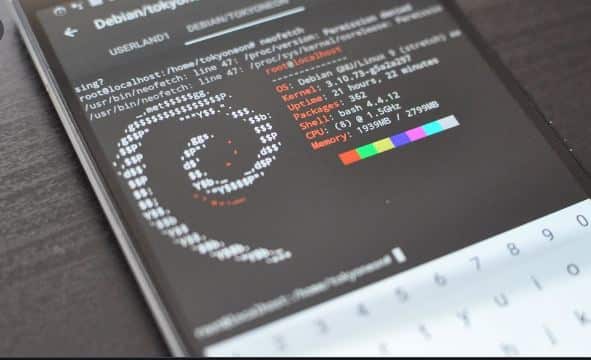
Hackode Download was developed by Ravi Kumar for penetration testers, ethical hackers, security researchers as well and security professionals. Use Hackode Apk to gather all the information regarding a target and to find valuable websites.
This is a great application with which thefts can
- Get information regarding other devices.
- Scan and find device or network vulnerabilities.
What is Hackode for Android Apk

It comes with in-built tools such as DNS Lookup, Ping, DNS diagnosis, Traceroute, security feed, and exploits monitoring. The best thing about this is that it does not require any rooted Android device. If you love using a cheesy interface, try this one. If you only have basic requirements, then this would work great for you.
Note: For this, you need to have a working internet connection.
As you open the application you shall see the following options:
- Exploit development and tools.
- Security feed.
- Scanning hosts and devices.
- Reconnaissance and data collection.
FEATURED: AndroRAT Old and New Version Download (APK File).
Hackode App New Features

- Reconnaissance: These are tools to gather information.
- Google Hacking: It carries modules that are used to find vulnerable websites. It has six different modules in it:
- PhpMyAdmin: This is used to bypass the username and passcode of the admin and takes one to the information schema tables of vulnerable sites directly.
- PhpConfig: This is used to show us Google search results that carry vulnerable websites which might allow one to include malicious files to a web app.
- SQL Injection: It shows all websites which are vulnerable to SQL injection attacks.
- MySQL Server: This shows us a search result that helps us get sensitive data from the target MySQL server.
- Login Portals: It shows us Google search result which carries simple SAMLphp login pages.
- Passcodes: It helps us to get files carrying SQL instructions where the administrator is sets a passcode for the database user.
- Whois Lookup: With this, we can see information on domain names or IPs. This usually includes information on the contact, technical information like DNS used for service, status information on the status of the site and type of server.
- Scanning: These are tools that are used to scan the target.
- Ping: This can be used to test the host’s reachability, and measure the round-trip time for messages sent from the host to the device.
- Traceroute: With this, we can identify intermediate devices and the connection’s speed.
- Mx Record: In this, we can get information regarding the target’s mail server which has the responsibility to accept mail messages on behalf of the recipient’s domain.
- DNS Dig: With this, we can find out information regarding the DNS server of the target site.
- Exploits: This has been in process since 2013 and we assume it shall stay like this.
- Security Feed: This is used to show the latest security news.
How To Use Hackode (Easy Tutorial)

- You first need to hack the application in steps.
- Once it has been installed, open it up.
- You shall see Google Hacking and Oops Lookup Tool under education.
- Select “Google hacking” and check the modules available.
- If you see information regarding the domain type and wish you have relevant details.
- Go to “scan module” and hit it. This one is used to provide us regarding the victim.
- Head towards “security” and the Metasploit tool can be used to scan security information and vulnerabilities.
Penetration Testing with Hackode
This simulated cyber attack is known as a pen test against the system to check out exploitable vulnerabilities. If we talk about web application security then is used to augment web application firewall (WAF).
This includes attempted breaching of any number of app systems, like application protocol interfaces (APIs), frontend or backend servers), and unsanitized inputs susceptible to code injection attacks.
Insights provided are then used to fine-tune WAF security policies, as well as patch, detected vulnerabilities.
Planning and Reconnaissance
- The scope and goal of the test are defined, including systems to be addressed and the use of testing methods.
- Intelligence is gathered such as names of networks and domains, mail servers, and much more so that one has a better understanding of how the target works and its potential vulnerabilities.
Scanning Whole Networks
This shows how the target app responds to different intrusion attempts. This can be done by:
- Static Analysis: Apps code is inspected to estimate how it behaves while running. This is used to scan the code that too in a single pass completely.
- Dynamic Analysis: This is used to inspect app code in the running state. This however seems to be more of a practical way to scan and also provide a real-time view into the app’s performance.
MITM Access
In this web application attacks are used like Cross-site scripting, SQL Backdoors and injections to uncover the target’s vulnerabilities which are then exploited by the testers, especially by escalating privileges, stealing data, intercepting traffic and much more to understand the damage they can cause.
It aims to see if vulnerability can achieve persistent presence in the exploited system long enough for bad actors to get in-depth access. The main goal is to imitate advanced persistent threats, which remain in the system for many months in order to steal sensitive data of the organization.
RECOMMENDED: SB Game Hacker Apk v5.2 Download.
Analyzing access levels
All the results from the test are then compiled into a report which details the following:
- Exploited vulnerabilities.
- Data that was accessed.
- Time in which the pen tester was able to be in the system without detection.
This information is then analyzed by the security personnel to configure the enterprise’s WAF settings and many other app security solutions in order to patch vulnerabilities and provide protection against future attacks.
ALSO CHECK: Download Freedom APK for Android 11/12.
Frequently Asked Questions
Is Hackode Pro real
No. This does not exist and you should not download such named apps.
Can it be used for social media accounts?
This cannot be used to hack Facebook. It is only an application to gather information and is not designed primarily to hack anything.
Can I find out the Wifi password with Hackode?
This cannot be used, for this, you need to use alternatives such as Aircrack-ng or Wireshark to achieve this.
Do I have to pay to use it?
This is a freeware app and requires no payments or subscriptions to use.
Hackode APK Free Download – #1 Android Hacking Tool
If you ever wanted every major security and ethical hacking tool in your pocket then download Hackode APK, it is that simple. It has over +100 famous tools including Nmap, Nessus and Kismet. Do let us know if you are starting out or if the tutorial above also helped you.
Release: v1.3.
Download Hackode APK Free (Latest Version)